eXtended Detection and Response (XDR)

Il trend degli attacchi cyber mostra una crescita costante non solo in termini di volumi ma anche in termini di sofisticazione.
Ogni organizzazione, specialmente se di piccola e media dimensione, non può far fronte da sola alle criticità derivanti dal monitoraggio della propria postura di sicurezza.
In un panorama di minacce informatiche in continua evoluzione, i sistemi di XDR si propongono di migliorare notevolmente i tempi di indagine e reazione dei team di sicurezza.
I sistemi XDR (eXtended Detection and Response) sono soluzioni di sicurezza che vanno oltre le “semplici” soluzioni di Endpoint Protection e EDR (Endpoint Detection and Response), integrando queste ultime con componenti per il controllo anche dei gateway di posta elettronica, dei servizi cloud e degli accessi.
I sistemi eXtended Detection and Response
Un XDR è uno strumento SaaS che offre una sicurezza olistica ottimizzata, integrando dati e prodotti di sicurezza in soluzioni semplificate: è una tecnologia di sicurezza multilivello che salvaguarda l’infrastruttura IT.
Mentre le aziende affrontano sempre di più un panorama di minacce in continua evoluzione e sfide complesse per la sicurezza con dipendenti in ambienti ibridi multi-cloud, l’XDR rappresenta una soluzione proattiva più efficiente.
A differenza di sistemi EDR, gli XDR ampliano l’ambito della sicurezza, integrando la protezione in una vasta serie di prodotti, tra cui gli endpoint di un’organizzazione, i server, le applicazioni cloud, le email e altro.
Un XDR combina prevenzione, rilevamento, indagine e risposta, fornendo visibilità, analisi, avvisi sugli incidenti correlati e risposte automatizzate per migliorare la sicurezza dei dati e combattere le minacce.
Raccoglie e correla i dati provenienti da più livelli di sicurezza come endpoint, app, email, cloud e reti, aumentando la visibilità sull’ambiente tecnologico di un’organizzazione.
Ciò consente ai team di sicurezza di rilevare, indagare e rispondere alle minacce informatiche in modo rapido ed efficace.
È importante usufruire di servizi XDR gestiti professionalmente e integrati in un SOC, in particolare nei casi di aziende piccole, medie o non strutturate, le quali spesso non hanno ingenti capacità di staff o infrastrutturali per gestire correttamente la sicurezza dei propri apparati.
Infatti, un servizio gestito ed integrato in un SOC allevia l’onere delle attività operative associate al monitoraggio, rilevazione e risposta ad attacchi cyber e riduce sensibilmente le spese associate alla gestione delle tecnologie, consentendo alle aziende di focalizzarsi sulle proprie attività “day-to-day” principali.
Come funziona un XDR?
L’XDR è fondamentalmente un consolidamento di strumenti e dati e rappresenta un importante passo avanti nelle funzionalità per la sicurezza aziendale.
Poiché l’XDR ha accesso ai dati non elaborati raccolti nell’ambiente, è in grado di rilevare attori malevoli che utilizzano software legittimo per accedere al sistema (cosa che il software di gestione degli eventi e delle informazioni sulla sicurezza, o SIEM, spesso non è in grado di fare).

L’XDR esegue l’analisi e la correlazione automatizzate dei dati delle attività, consentendo ai team di sicurezza di contenere le minacce in modo più efficace.
È ad esempio in grado di coprire rilevamenti di rete, lateral movement, connessioni anomale, beacon, esfiltrazione e distribuzione di artefatti malevoli.
Analogamente all’EDR, l’XDR risponde alla minaccia per contenerla e rimuoverla.
Tuttavia, il livello superiore di raccolta dei dati e integrazione con l’ambiente dell’XDR consente di rispondere in modo più efficace alla risorsa interessata.
Le piattaforme XDR forniscono la visibilità e il contesto olistici di cui gli analisti della sicurezza hanno bisogno per rispondere alle minacce in modo mirato ed efficace.
Questa risposta su misura aiuta a contenere non solo la minaccia stessa, ma anche l’impatto della risposta sui sistemi, ad esempio riducendo il downtime sui server critici.
L’XDR è composto da tre elementi operativi: telemetria e analisi dei dati, rilevamento e risposta.
Telemetria e analisi dei dati
L’XDR monitora e raccoglie i dati su più layer di sicurezza, tra cui endpoint, rete, server e cloud.
L’analisi dei dati viene utilizzata per correlare il contesto di migliaia di avvisi da questi layer in modo da far emergere un numero inferiore di avvisi ad alta priorità, contribuendo a evitare il sovraccarico dei team di sicurezza.
Rilevamento
La visibilità superiore dell’XDR consente di vagliare gli avvisi e segnalare quelli che richiedono una risposta.
La stessa visibilità consente di creare basi di confronto del comportamento normale all’interno di un ambiente per consentire il rilevamento di minacce che utilizzano al meglio software, porte e protocolli e di indagare sull’origine della minaccia per impedire che influisca su altre parti del sistema.
Risposta
Proprio come l’EDR, l’XDR ha la capacità di contenere e rimuovere le minacce rilevate, nonché di aggiornare le policy di sicurezza per impedire il ripetersi di violazioni simili.
Tuttavia, a differenza dell’EDR, che svolge questa funzione solo su endpoint e carichi di lavoro, l’XDR va oltre la protezione degli endpoint per rispondere alle minacce in tutti i punti di controllo della sicurezza che tocca, dalla sicurezza dei container alle reti e ai server.
Infatti, mentre l’EDR si concentra sugli endpoint, l’XDR amplia il raggio d’azione concentrandosi su vari punti di controllo della sicurezza per rilevare le minacce più rapidamente, utilizzando analisi approfondite e l’automazione.
XDR vs. EDR
L’XDR rappresenta l’evoluzione del rilevamento e della risposta oltre l’attuale approccio con soluzione specifica e per vettore singolo.
Chiaramente, il rilevamento e la risposta sugli endpoint (EDR) sono stati estremamente preziosi.
Tuttavia, nonostante la profondità della sua capacità, l’EDR è limitato perché può solo esaminare e rispondere alle minacce sugli endpoint gestiti.

Ciò limita l’ambito delle minacce che possono essere rilevate, nonché la visione di chi e cosa è stato impattato, limitando l’efficacia della risposta all’interno del SOC.
Allo stesso modo, la competenza degli strumenti di Network Traffic Analysis (NTA) è limitata alla rete e ai segmenti di rete monitorati e tende a generare una grande quantità di log.
La correlazione tra avvisi di rete e altri dati di attività è invece fondamentale per dare un senso e incrementare il valore derivante dagli avvisi stessi di rete.
I sistemi XDR fungono quindi come alternativa alle soluzioni limitate a un solo livello di sicurezza o in grado di eseguire solo la correlazione degli eventi senza risposta, di fatto ponendosi come l’evoluzione di soluzioni quali Endpoint Detection and Response e Network Traffic Analysis.
Sebbene siano ancora utili, questi ultimi strumenti tendono a generare maggiori volumi di avvisi, ma richiedono più tempo per indagare e rispondere agli eventi e maggiore manutenzione e gestione.
Al contrario, un sistema XDR consolida gli strumenti e consente ai team di sicurezza di lavorare in modo più efficace ed efficiente.
Affidarsi ad una tecnologia XDR significa creare un vantaggio di sicurezza, migliorando le capacità di rilevamento e reazione e unificando visibilità e controllo a livello di endpoint, rete e cloud.
Collegando i dati provenienti da diverse tipologie di soluzioni di sicurezza, la visibilità sulle minacce risulta migliorata e i tempi per la rilevazione e risposta agli attacchi si riducono.
Gli XDR facilitano, infatti, l’indagine avanzata e le capacità di ricerca delle minacce su più domini da una unica console.
TelsyDefenX: il servizio gestito di XDR
TelsyDefenX è il servizio adatto ad ogni organizzazione che ricerchi un partner specializzato in cybersicurezza per un servizio di monitoraggio, investigazione e response centralizzato e correlato per la propria infrastruttura ICT: una soluzione all-in-one semplice da implementare e con supporto dedicato end-to-end.
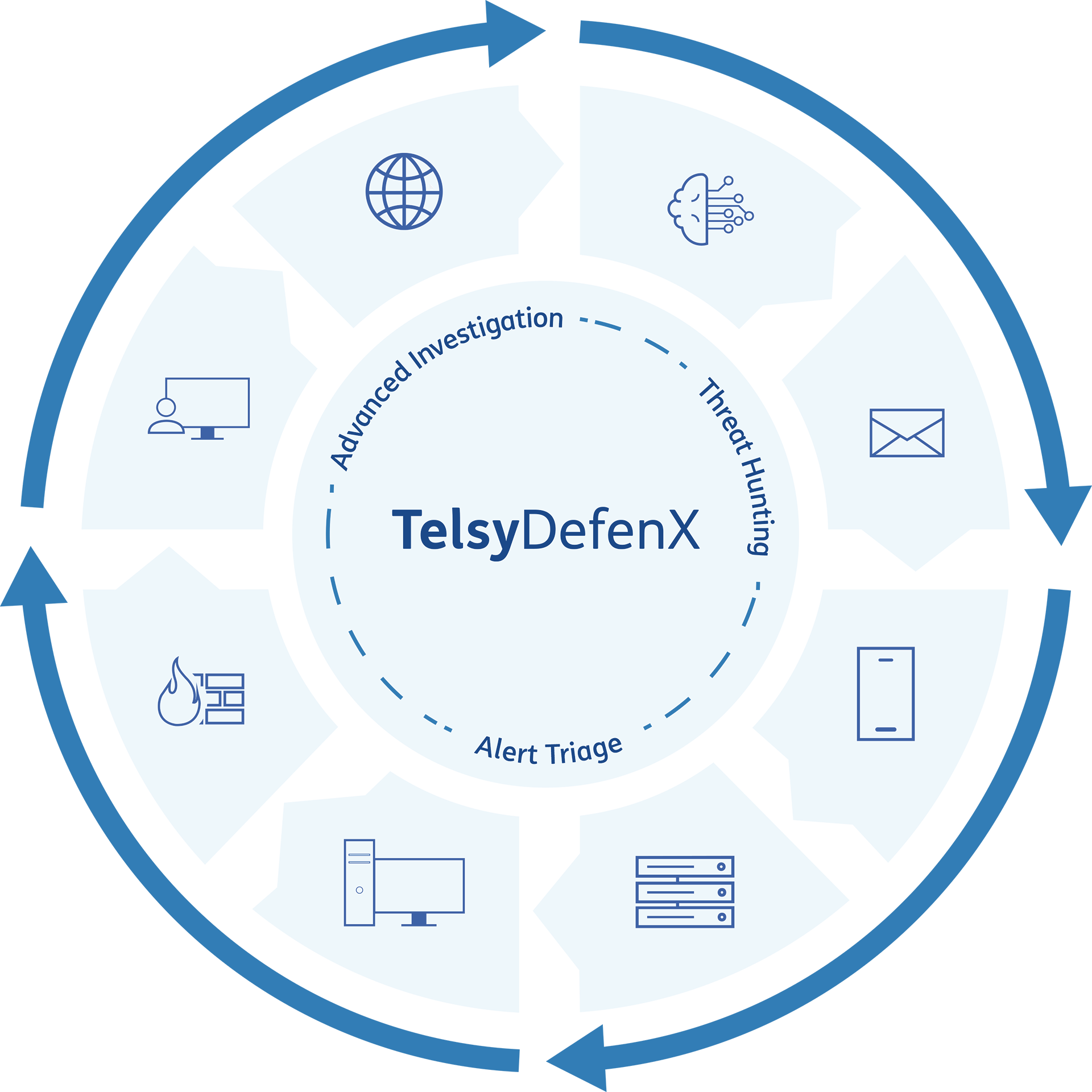 È un servizio gestito che sfrutta le tecnologie di eXtended Detection and Response (XDR) integrandole sul SOC aziendale di Telsy per fornire sicurezza e protezione contro le minacce informatiche e i pericoli correlati, supportando nelle sue attività il personale tecnico dedicato alla difesa cyber dell’organizzazione.
È un servizio gestito che sfrutta le tecnologie di eXtended Detection and Response (XDR) integrandole sul SOC aziendale di Telsy per fornire sicurezza e protezione contro le minacce informatiche e i pericoli correlati, supportando nelle sue attività il personale tecnico dedicato alla difesa cyber dell’organizzazione.
TelsyDefenX mette a disposizione dei clienti un servizio gestito di identificazione, investigazione, protezione e response estesa che, tramite la collezione e la correlazione delle informazioni provenienti da email, PdL, server, cloud, mobile e network, abilita una visione completa sull’infrastruttura ICT delle organizzazioni, accelerando i processi di investigation ed efficientando le attività di monitoraggio e response da parte dell’iSOC di Telsy.
Il valore aggiunto della soluzione risiede nei servizi di affiancamento e supporto al cliente nelle fasi di on-boarding & start-up servizio, insieme al servizio (operativo 24H) di alert management e alle funzioni di threat investigation & reporting che eroghiamo attraverso il nostro SOC.
TelsyDefenX è pensato per chi teme di incorrere in un cyber incident o un data breach, soprattutto se utilizza una moltitudine di soluzioni di protezione frammentate e non integrate che non riesce a gestire in autonomia, anche per scarsità di risorse di staff dedicate.
Perchè TelsyDefenX
TelsyDefenX è una soluzione “all-in-one” che supera i modelli difesa verticali con un approccio centralizzato ed integrato con supporto dedicato end-to-end.
L’expertise di Telsy garantisce affiancamento da parte del nostro team di cybersecurity specialists del SOC, con un monitoraggio degli alert 24/7, una gestione proattiva delle anomalie e supporto in caso di incidenti cyber.
Inoltre, viene garantita protezione avanzata ed estesa grazie alla combinazione dell’intelligence umana a quella tecnologica, proteggendo efficacemente da attacchi hacker di diversa natura, tra cui ransomware, phishing e BEC verso PdL, server, email, cloud, network e dispositivi mobili.
Scarica la brochure di TelsyDefenX.
Scopri di più su questa e altre soluzioni di Managed Detection & Response di Telsy.
