NOKIA IMPACT WEB PLATFORM – Responsible Vulnerabilities Disclosure
During some activities of the Telsy research team within a client company, some vulnerabilities emerged in the product NOKIA IMPACT WEB PLATFORM.
These vulnerabilities are currently identified according to the following CVEs :
CVE-2019-17403, CVE-2019-17404, CVE-2019-17405 and CVE -2019-17406.
The concatenation of some of them (unrestricted file upload, path traversal and full path disclosure) led to post-auth remote execution of arbitrary code (RCE) in the context of the same product.
CVE-2019-17403 – NOKIA IMPACT < 18A – Unrestricted File Upload:
An authenticated user, with access to the deviceImport function, is able to upload arbitrary files on arbitary positions on the webserver filesystem, reaching remote code execution. The file extension is also not fitered, allowing the upload of files with arbitrary extensions (Unrestricted File Upload).
CVE-2019-17406 – NOKIA IMPACT < 18A – Path Traversal:
The filename parameter is vulnerable to a path traversal vulnerability, indeed naming the file as a relative path an attacker is able to save it in an arbitary position on the filesystem (e.g ../../../../../../../tmp/myfile.csv)
CVE-2019-17404 – NOKIA IMPACT < 18A – Full Path Disclosure:
If the path traversal is exploited to point to a non-existent path the application will throw an unhandled exception, leaking the full path of where the files are saved (Full path disclosure).
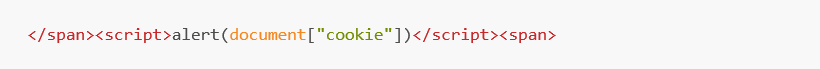
CVE-2019-17405 – NOKIA IMPACT < 18A – Cross Site Scripting:
A Reflected self XSS was found in the searchbox inside the Manual page at: https://[host]/ui/help/en_US/[redacted]ConsoleHelp/index
The payload used is:
// PoC
We published a PoC chaining three of the vulnerabilities described. It’s available on our GitHub page
